Unveiling the Mystery: What is The Genius Wave? At the heart of many success stories lately is The Genius Wave,...
In the world of lottery games, winning big has always been a dream for many, but often seemed like an...
Cybersecurity researchers have discovered multiple campaigns targeting Docker Hub by planting millions of malicious "imageless" containers over the past five years, once again underscoring...
The U.S. government has unveiled new security guidelines aimed at bolstering critical infrastructure against artificial intelligence (AI)-related threats. "These guidelines...
The U.K. National Cyber Security Centre (NCSC) is calling on manufacturers of smart devices to comply with new legislation that prohibits them from...
Google on Monday revealed that almost 200,000 app submissions to its Play Store for Android were either rejected or remediated...
A previously undocumented cyber threat dubbed Muddling Meerkat has been observed undertaking sophisticated domain name system (DNS) activities in a likely effort to evade...
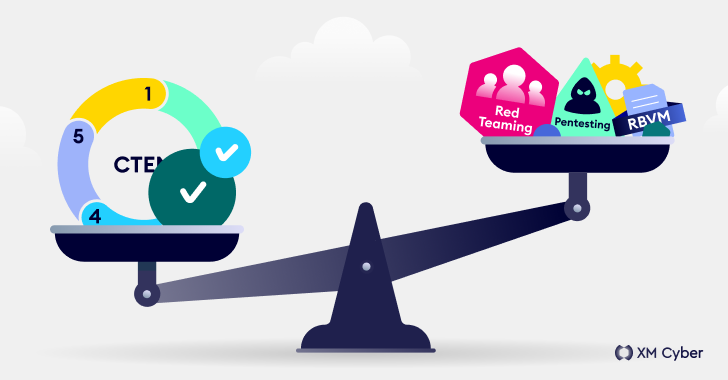
Navigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
It comes as no surprise that today's cyber threats are orders of magnitude more complex than those of the past. And the ever-evolving tactics...
A security vulnerability has been discovered in the R programming language that could be exploited by a threat actor to create a...
Multiple critical security flaws have been disclosed in the Judge0 open-source online code execution system that could be exploited to obtain code execution on...